What is VPN Protocols?
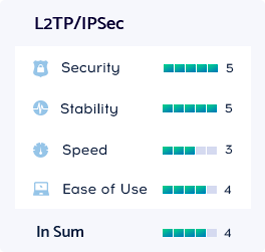
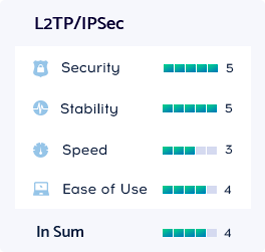
The VPN protocol you use will determine how your data is routed between your computer and the VPN servers. Each one of the protocols has different configurations which are beneficial in a variety of circumstances according to the situation. For example, some of them give priority to speed, while others focus on privacy and security. We offer 1 most convient and safe protocol: L2TP/IPSec.
L2TP/IPSec
The Layer 2 Tunneling Protocol is a very popular VPN protocol. L2TP doesn’t include data encryption, which is why we implemented the IPSec technology. After implementing L2TP/IPSec, it becomes one of the most secure and dependable VPN connections. L2TP/IPSec uses the AES-256-bit encryption and has no known vulnerabilities. IPsec is a set of protocols for data protection transmitted over the Internet Protocol (IP). It offers integrity authentication checkup and it also supports the encryption of IP packets.
3 simultaneous connections